Why Small Businesses Still Get Breached
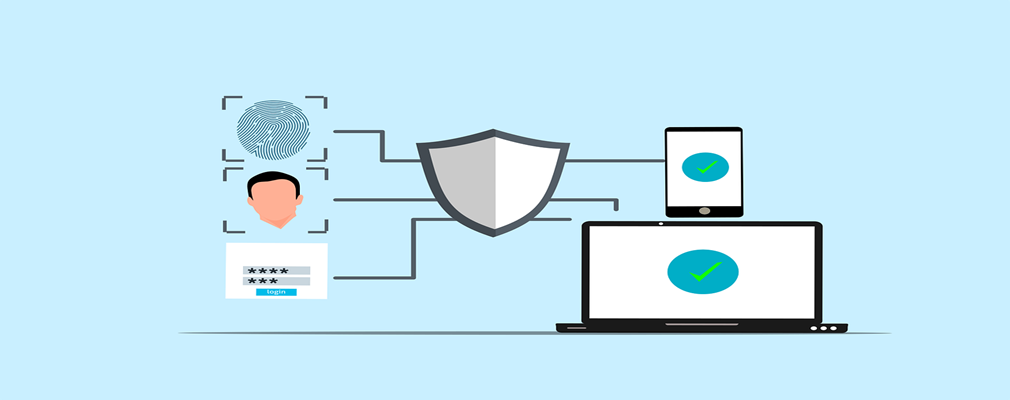
Most small businesses don’t suffer security incidents because they “have no security.”
They get breached because one stolen password ends up unlocking far more than it should.
That’s the weakness of the old castle‑and‑moat security model. Once someone gets past the perimeter—usually through a compromised login—they can often move through systems, apps, and data with very few additional checks.